Generative AI
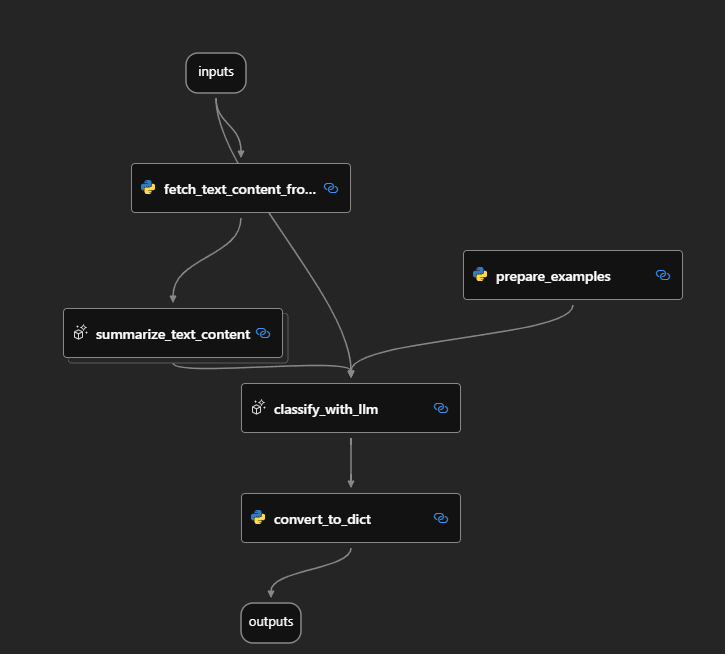
Revolutionizing AI Apps: The Power of MLflow AI Gateway & Llama 2!
02 Sep 23
11m read.
AI Transformation
Generative AI
Supercharge productivity with Large Language Models (LLMs)
26 Aug 23
18m read.
AI Transformation
trending
editors-pick
Generative AI
Enter the world of Generative AI
18 Aug 23
43m read.